Or “How I Learned to Stop Worrying and Sign My Requests”
By Rob Hazan, Senior Director of Product, Index Exchange
In the decade I’ve worked in ad tech, I’ve witnessed a pattern: where the money goes, fraud follows. Right now, CTV is where the money’s going. It’s a programmatic environment with tens of billions in ad spend, CPMs up to 25x greater than web ads, and relatively immature standards. Layer in the fact that the invalid traffic (IVT) detection techniques that evolved for the web don’t work as well in CTV, and you have the perfect conditions for fraudsters to engage in scheme after scheme after scheme after scheme.
Over the past decade, programmatic advertising has provided marketers with the opportunity to access highly efficient, measurable, and scalable advertising opportunities for web and mobile app consumers. As television now digitizes, our industry is presented with a great opportunity: to bring the benefits of programmatic ads to the most immersive content and advertising medium. But we can’t get there with a compromised supply chain.
For decades, TV media owners and buyers have relied on direct relationships and face-to-face accountability to drive their ad businesses. They’re justifiably wary of handing over a $150+ billion business to programmatic ad tech. As these ad businesses modernize, they’ve used deals and ad server priorities to replicate the offline behaviors they’re comfortable with. By doing this, they’ve degraded their ability to reach consumers, fulfill ad budgets, and develop data-driven solutions – they’ve opted for peace of mind. Replicating legacy TV buying behavior has enabled CTV growth for now, but as buyers increase their programmatic CTV ad spending with dollars shifted from linear TV budgets, now is the time to deliver on ad tech’s promise: giving buyers all the efficiencies and benefits of a programmatic marketplace while also giving them peace of mind.
The bad guys lie.
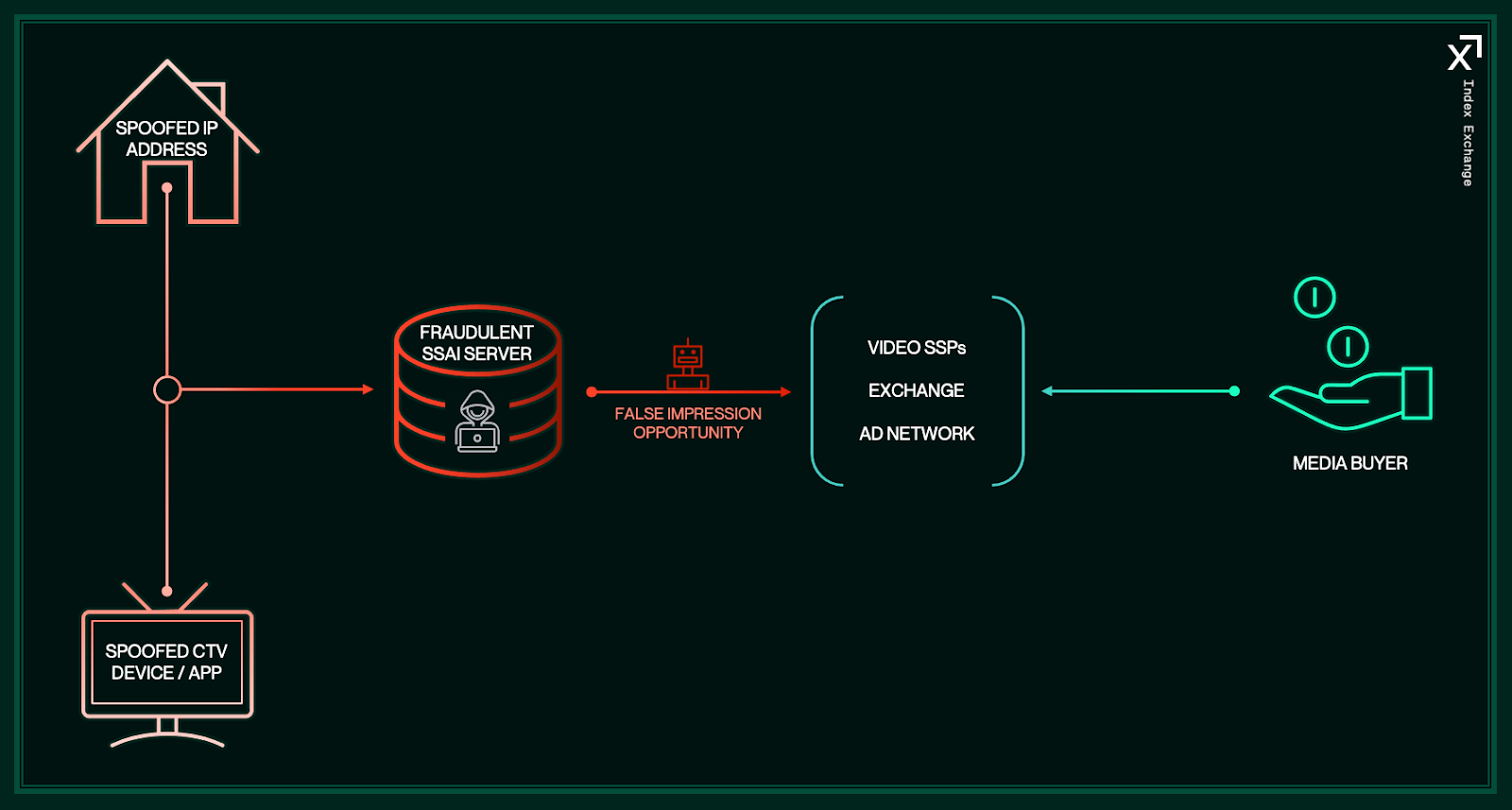
CTV fraud schemes tend to lie about two things: the device/app generating the impression, and the seller. For example, one scheme is to buy cheap supply and resell it at a premium by falsifying bid requests to make it look like the seller is a well-known streaming app. Another is to impersonate a legitimate party, like a server-side ad insertion (SSAI) vendor, and generate requests from non-existent devices and apps – a process known as “spoofing”:
In addition to the familiar pattern (where the money goes, fraud follows), it’s also clear that ad tech’s solutions are almost always reactive, rather than proactive. Scammers tend to stay one step ahead until the effort and costs required to execute their schemes outweigh the economic incentive. So where do we start?
The answer is crypto
(AND NO, I DON’T MEAN BLOCKCHAIN)
Probably not the kind you’re thinking of…
Digital cryptographic signing has been around since the late 1980s, and it’s widely deployed in financial services, where advanced security is foundational. It validates the source of a message by providing the recipient with a private key that pairs with the sender’s public key. This technology is the best tool we have for validating that CTV impression events such as bid requests, impression notifications, and user interactions are triggered by real people using legitimate devices to view content and ads from media owners authorized to sell the inventory.
Here’s an example of how this could work:
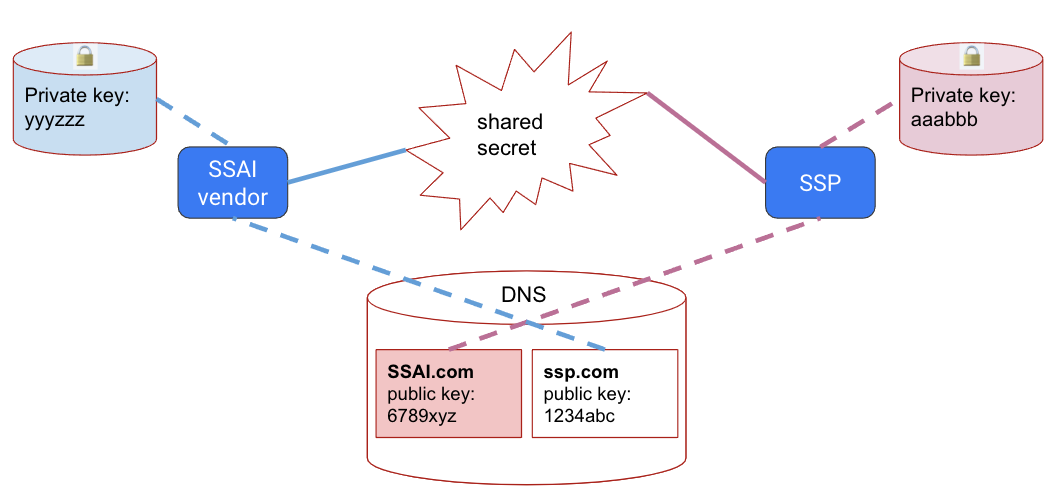
The SSAI vendor and an SSP in the supply chain each generate a public/private cryptographic key-pair and publish their public keys via a Domain Name System (DNS) entry associated with their ad serving domains. Using these keys, both parties calculate a shared secret to produce signatures for their server-to-server communications. This way, when the SSAI vendor receives an ad from this SSP, the impression notification it sends will include its digital signature in the HTTP Header, allowing the SSP to use the same shared secret to confirm the identity of the SSAI vendor:
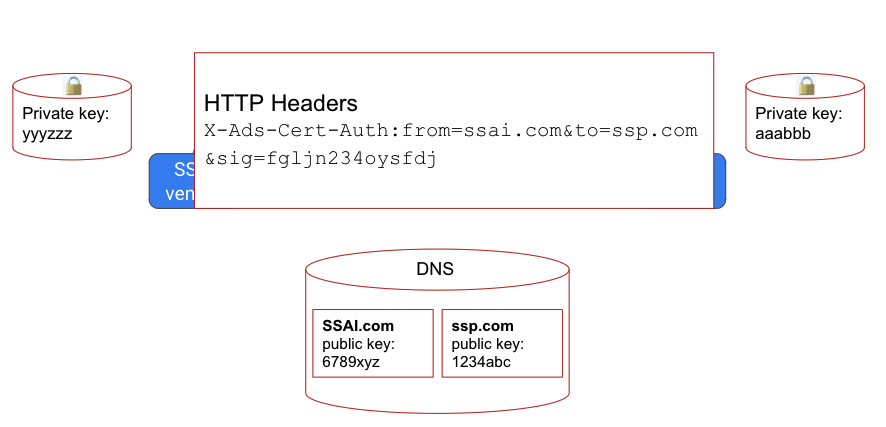
In the above scenario, third parties can’t calculate the shared secret, making it impossible for scammers to correctly sign impression notifications. So long as the private keys and shared secret remain a secret, only the SSAI vendor and the SSP will be able to authenticate their communications, making an incorrect or missing signature a clear signal to the SSP that something is amiss with the supply. By securing each link in the supply chain in this manner, we can make it impractical for scammers to impersonate legitimate parties, remove the financial incentive to generate IVT, and increase buyer confidence in the validity of CTV inventory.
It takes a village.
A problem of this magnitude requires an industry-wide solution, and the IAB Tech Lab’s formation of the Security Foundations Working Group is a significant step toward this end. Engineering and Product leaders from across our industry have come together to propose a new ads.cert protocol suite that’s generic enough to address numerous ad tech use cases, but designed specifically with CTV in mind. The proposal includes:
- Call Signs: A spec for the publishing and management of public cryptographic keys by ad tech participants.
- Authenticated Connections: A spec for authenticated server-to-server communication.
- Authenticated Delivery: A spec for creating a tamper-evident seal on transactions through the programmatic supply chain.
- Authenticated Devices: A spec for authenticating the devices that emit ad requests.
Index Exchange joined hands with Publica, Google Display & Video 360, and Oracle(Moat) to build a proof of concept for the Authenticated Connections protocol, and in joint testing, we were able to detect several scenarios:
- Impression notifications sent with valid signatures
- Impression notifications sent with invalid signatures
- Impression notifications sent without signatures
Following our successful proof of concept, we’ve joined the IAB Tech Lab in recommending that all ad tech participants, SSAI vendors, SSPs, DSPs and measurement providers establish an ads.cert Call Sign – a quick and simple measure that qualifies you to participate in ads.cert.
For those looking to take a more active step in the fight against CTV fraudsters, we encourage you to begin signing and validating impression notifications using Authenticated Connections. To make adoption easy, we’ve created an ads.cert open source software repository with implementations for Call Signs and Authenticated Connections. Adoption of these standards is a meaningful step towards increasing confidence with TV buyers as they look to transition their spend from linear to digital.
What’s next for the Security Foundations Working Group?
This year, we’ll test a proof of concept for ads.cert Authenticated Delivery to generate a tamper-evident seal that confirms a transaction hasn’t been compromised. We’re also developing the ads.cert Authenticated Devices protocol to further secure CTV transactions with the help of hardware OEMs – an effective tool for eliminating bots, device farms, supply misrepresentation, and other forms of sophisticated IVT.
ABOUT THE AUTHOR

Rob Hazan
Senior Director of Product
Index Exchange